How to reduce failed payouts by up to 70% using payment pre-validation - without rebuilding your payout stack.
by Suchi Sraba Pattanayak. Suchi Pattanayak is a Product Director at Nium, where he owns product strategy for account verification and global payouts. With 7 years in fintech across Visa and Nium, he focuses on making cross-border money movement reliable, fraud-resistant, and operationally efficient. IIM Bangalore MBA | NIT Rourkela B.Tech.
TLDR: Payment pre-validation reduces payout failure rates by up to 70% by catching invalid accounts, closed accounts, and name mismatches before funds are released. In Nium's payout network, 77% of all payment returns trace to incorrect or closed account numbers and name mismatches - failures that are entirely preventable with a verification check run before the payment leaves the system. This guide covers how payout failures occur, what they cost, and how to design a prevention-first approach without rebuilding your payout stack.
The problem every payout team knows too well: Three ways payout failures play out in practice
Every payout operations team has a version of this story.
A payroll batch runs on Friday. By Monday morning, a percentage of those payments have returned. By Tuesday, your ops team is working through exception reports - manually re-routing failed payments, contacting employees to confirm bank details, and triggering re-runs. Some of those payments won’t land until Thursday.
Payroll and vendor payments
For employees waiting on salary, it’s an unacceptable delay. For your ops team, it’s a half-week of avoidable fire-fighting.
Delayed salary or vendor payouts don’t just create operational overhead. They drive HR escalations, vendor friction, and recurring “war rooms” every pay cycle.
Marketplaces and creator platforms
Now take a different scenario.
A marketplace with 50,000 sellers sees an 8% payout hold rate during onboarding — accounts flagged because the bank details submitted don’t match what’s on file at the bank. Ops and support teams spend hours each week unlocking holds, chasing bank statements, and manually overriding issues.
Sellers churn. Some move to competitors.
Payout holds directly impact activation, trust, and GMV. Each failed payout becomes a reason to try another platform.
Fintech and remittance providers
Or consider a cross-border fintech operating across Southeast Asia and LatAm.
First-time payouts to new beneficiaries fail at 3–4%. Each failure triggers a manual investigation. Re-processing adds cost. Compliance teams field RFIs. Leadership starts asking why STP rates are declining.
Failed payouts don’t just create operational friction. They introduce FX losses, increase compliance exposure, and reduce payment success rates in key corridors.
The common thread
Across all of these scenarios, the failures were preventable.
The bank account details were already incorrect before the payout was sent. A simple verification check, run before the payment, would have caught the mismatch and flagged it for correction.
The payout would never have left the system with bad data.
This guide will cover:
1. Understanding why payouts fail — and what it’s really costing you
- Most payout failures are caused by bad data — not broken systems
- The real cost of failed payouts — and how many are preventable
2. Designing a prevention-first approach — and how it fits into your workflow
- Where bad data enters your system and how to catch it early
- Why most verification methods fall short at scale
- How to add verification into onboarding, batch, and payout flows
3. Choosing the right verification approach
- What good verification should actually tell you
- Why coverage determines how effective verification is
- How Nium Verify combines coverage, speed, and simplicity
4. Implementation, ROI, and next steps
- What implementation looks like — and how quickly you can go live
- The ROI of preventing failures before they happen
- How to decide if pre-payout verification is right for you
_________________________________________________________
Most payout failures are caused by bad data - not broken systems
Most payout failures aren’t caused by network outages, banking infrastructure, or regulatory blocks. They’re caused by bad data — wrong account numbers, mismatched names, closed accounts, and outdated routing codes that are already incorrect when the payment is released.
Industry data consistently shows the same pattern:
| Cause | % of Returns (Typical) |
| Wrong or closed account number | ~30–35% |
| Name mismatch (payee name ≠ account holder name) | ~10–15% |
| Invalid routing code / sort code / IFSC | ~15–20% |
| Dormant or frozen account | ~10% |
| Compliance reject | ~5–10% |
| Other (network, bank-side, currency mismatch) | ~10–15% |
In Nium's own payout network, 77% of all payment returns are attributable to incorrect or closed account numbers and name mismatches alone. These are not infrastructure failures. They are data failures — and data failures are preventable.
Bad account data enters your system in predictable ways
Bad account data typically enters payout systems through three channels:
1. Self-submitted details: Users enter their own bank details during onboarding. Typos, transpositions, and outdated accounts are common — and rarely checked in real time.
2. Aging payee databases: Accounts that were valid months ago may no longer be active. Without periodic verification, your database slowly decays.
3. Fraud and manipulated details: Payment redirection fraud, where attackers replace legitimate bank details, accounts for billions in losses annually. Many of these attacks succeed because no verification check is performed after details are changed.
The real cost of failed payouts is higher than most teams think
Most teams think of failed payments as a volume problem — a small percentage of transactions that return and get re-processed. The actual cost is significantly larger, and most of it is invisible on the balance sheet.
- For payroll & vendor payments: Each failed payout is two costs: the re-run itself and the internal time spent resolving HR/vendor escalations.
- For marketplaces & creator platforms: The real cost is not just support tickets — it's churned sellers, creators, and partners whose first payout experience was a failure.
- For cross-border fintech & remittance: Corridor-level failure hotspots increase FX noise, compliance RFIs, and regulatory scrutiny in your growth markets.
Most teams treat failed payments as a small percentage problem. The reality is that the true cost is much larger — and mostly hidden.
Direct costs
- Re-processing fees
- Wire recall fees
- FX re-exposure
Indirect costs
- Ops team time
- Customer and payee trust
- Compliance overhead
- Downstream settlement risk
For example: A team processing 500 payouts per day at a 1.5% failure rate generates ~165 exceptions per month. At $25 per incident, that’s $4,100/month in hidden operational cost.
The metric that matters: how many failures were preventable?
For account-detail failures — wrong account numbers, invalid routing codes, name mismatches, closed accounts — the answer is close to 100%. These are not probabilistic failures. They are deterministic: if the account does not exist or the name does not match, the payment will fail. You can know this before releasing the payment. The only question is whether you choose to check.
_________________________________________________________
There are two ways to handle payout failure
Detection after the fact
Send the payment → wait for failure → investigate → re-process
Prevention before release
Verify account details → catch issues → fix before sending
The economics of prevention versus detection are not close:
| Detection (after the fact) | Prevention (before release) | |
|
Cost per incident |
$15–50 (ops handling + re-processing) | $0.15–0.50 (verification API call) |
| Time to resolve | Hours to days | Seconds (flagged before release) |
| Payee experience | Delayed payment, possible hold | Proactive correction, no disruption |
| Fraud exposure | Payment exits system before detection | Mismatch caught before payment leaves |
| Compliance exposure | Potential RFI, reporting obligation | Risk removed before transaction |
At scale, the cost differential is not marginal. A payout operation processing 10,000 payments per month at a 1.5% failure rate — with the average handling cost of $25 per exception — is spending $3,750/month on avoidable exceptions. At $0.25 per verification, preventing those same failures costs $2,500/month to verify all payments — and saves the exceptions entirely. Net saving: $1,250/month, before factoring in FX risk, compliance overhead, or payee experience impact.
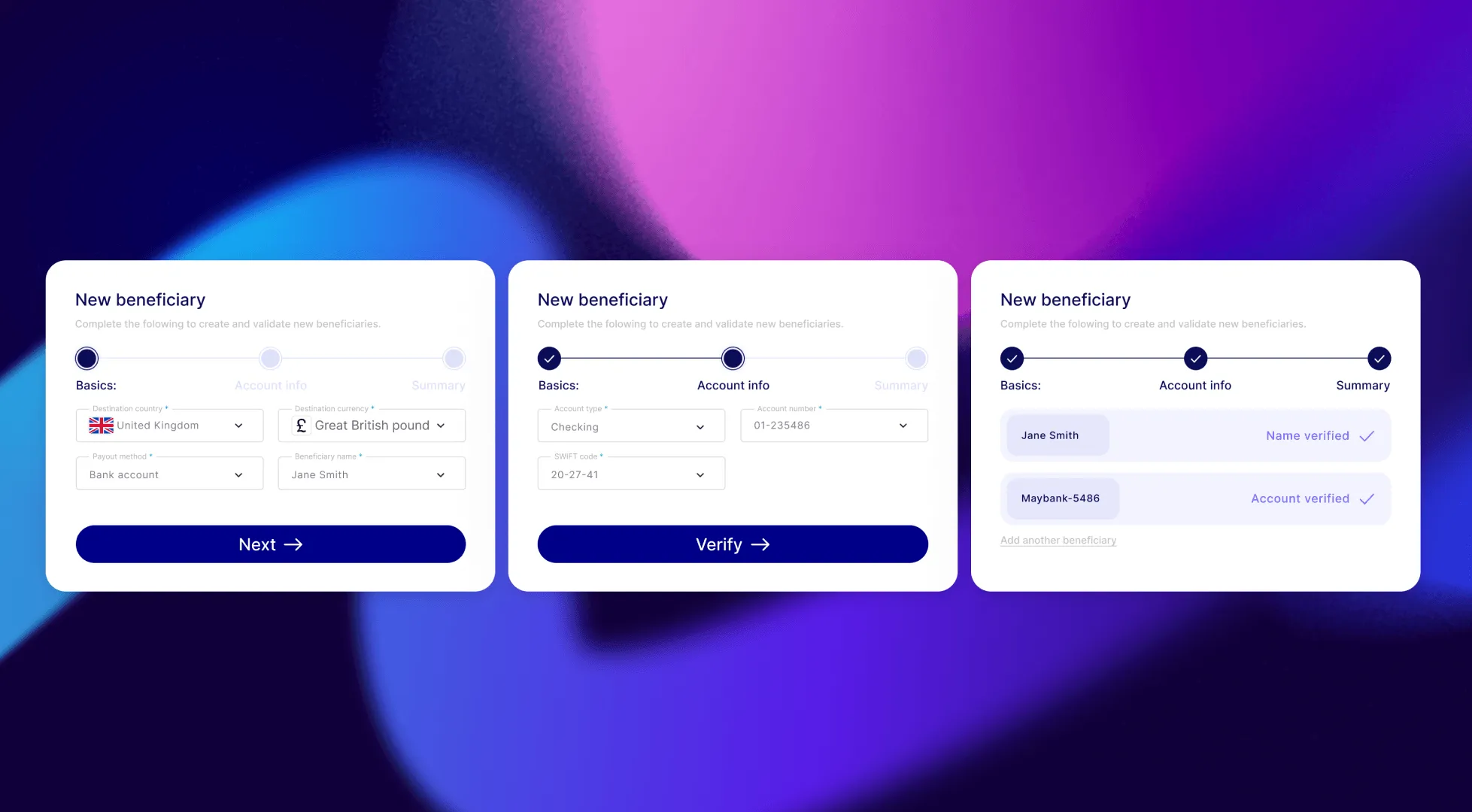
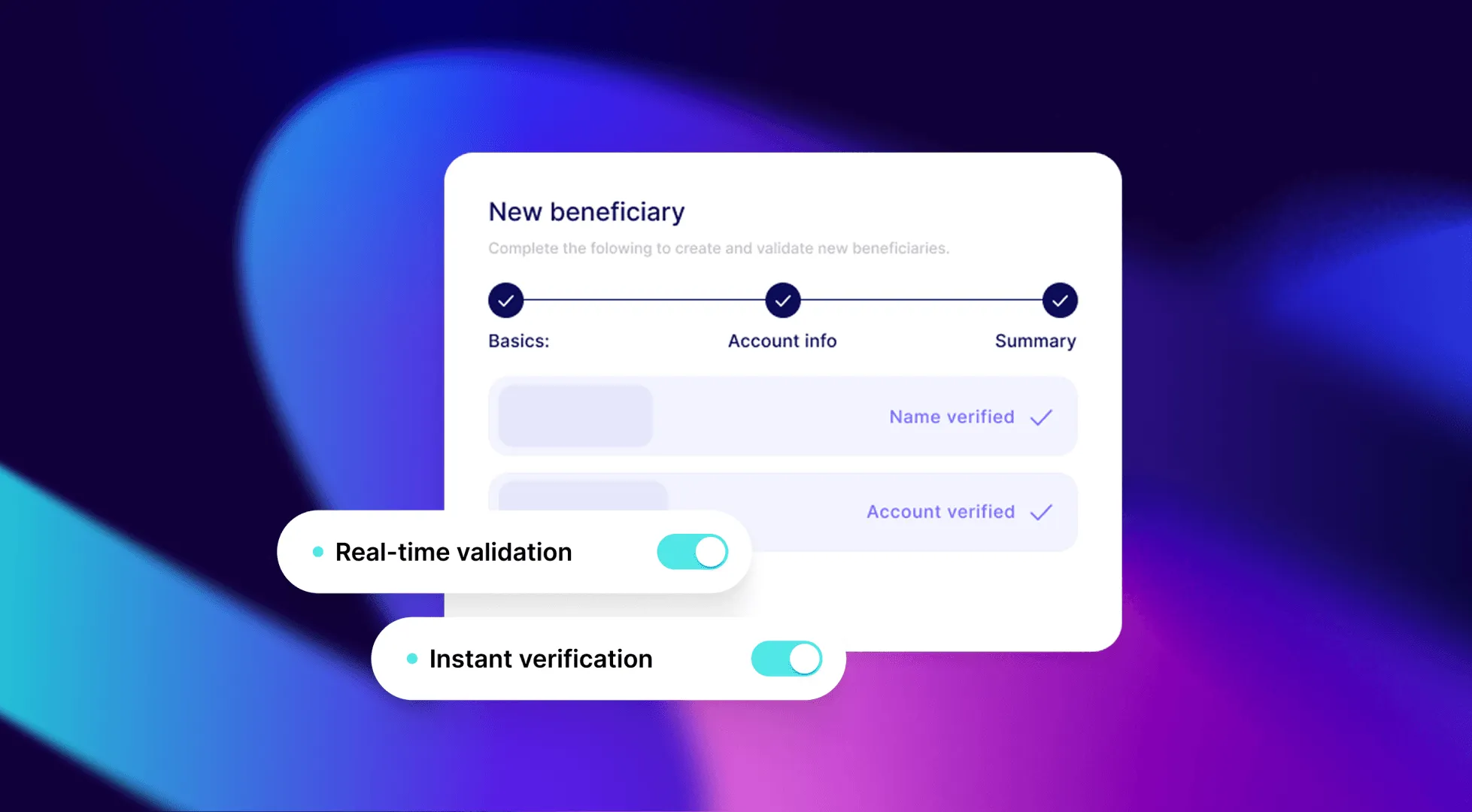
What is payment pre-validation?
Payment pre-validation also referred to as beneficiary validation or account pre-validation is a process in which a payment platform confirms that a recipient's bank account number, routing code, and account holder name are valid and active before releasing a payment. The check is performed via a real-time API call to a verification provider, which returns a status (valid or invalid), a failure reason code, and, where supported, a name-match score against the bank's registered account holder name. The purpose is to prevent payment returns caused by bad account data rather than resolve them after the fact.
_________________________________________________________
Reducing failures starts with one design decision: A checklist
Reducing failures starts with one design decision
If your goal is to reduce failed payments, the key question is:
Where will you catch bad data before release?
- Map failure reasons to data issues
- Pull your return reason codes.
- If >30% are account-detail issues (invalid account, routing, name mismatch), you have a preventable failure problem.
- Identify all entry points for bank details
- Self-serve onboarding, batch uploads, support-initiated changes, file integrations.
- Choose one or more verification triggers
- Onboarding, pre-flight batch runs, webhook on change, periodic hygiene.
- Decide verification coverage
- Start with high-volume / high-failure corridors.
- Define routing rules for verification responses
- Auto-approve, block, or send to manual review based on status and name-match score.
The next sections walk through the main verification approaches and where to insert them in your workflow.
_________________________________________________________
Not all verification methods are built for scale
Not all verification methods are equal. Teams evaluating this space typically encounter three options:
Trial deposits are slow and operationally heavy
- Takes 1–3 days
- Requires reconciliation
- No name validation
- Adds onboarding friction
Manual verification does not scale
- Requires human review
- Prone to fraud
- High friction for users
- Breaks at volume
Real-time API verification enables prevention
- Real-time response
- No test payments
- Name matching where supported
- Scales across workflows
- Actionable response data
_________________________________________________________
See what failed payouts are costing you
Before choosing an approach, quantify your baseline.
Use the Nium Verify ROI Calculator to:
- Estimate failure volume
- Identify preventable failures
- Model potential savings
Most teams get a clear business case in under 2 minutes.
_________________________________________________________
You can add verification without rebuilding your stack
Verification is a lightweight layer that fits into your existing payout workflows — no rebuild required.
You can add it at four key points:
1. Onboarding — catch bad data at entry
Verify bank details when a payee is created. Invalid or mismatched details are flagged immediately, so they can be corrected before any payment is attempted.
Best for: marketplaces, payroll platforms, and onboarding new employees or sellers
2. Before payout — validate your batch
Run verification before releasing a payout batch. Invalid accounts are removed upfront, so payments go out clean and exceptions are handled separately.
Best for: payroll runs, vendor payments, and scheduled payout cycles
3. On change — prevent fraud and errors
Re-verify whenever bank details are updated. This ensures new account details match the intended payee before the next payment is sent.
Best for: platforms handling bank detail updates or change requests
4. Ongoing — keep your data clean
Periodically re-verify stored accounts to catch closed, inactive, or changed details before they cause failures.
Best for: large payee databases with recurring payouts
_________________________________________________________
A modern verification should provide all of the information you need
A modern bank account verification API should return more than a binary valid/invalid result. The data richness of the response determines how actionable the verification is:
| Response Field | What It Tells You | How to Use It |
| status | valid/invalid | Gate the payout: only release if valid |
| failureCode | Specific reason for failure (account closed, invalid routing, etc.) | Route to correct exception workflow by failure type |
| accountHolderName | Name registered at the bank | Compare against your payee name on file |
| nameMatch | full / partial / no match | Trigger manual review for partial; block for no match |
| derivedAccountHolderName | Bank-provided correct name | Prompt payee to update their profile with the correct name |
| accountStatus | active / closed / restricted | Distinguish between "account doesn't exist" and "account restricted" |
The difference between a binary response and a rich response is the difference between "we can't pay this" and "the account is closed — here's the correct name registered at the bank, please update the payee's profile."
_________________________________________________________
Verification is only as strong as the coverage you have
Bank account verification coverage varies by market and method. The key coverage dimensions to evaluate:
- Account existence check: Does the account exist and can it receive funds? Available in most major corridors.
- Name match: Does the account holder name match the payee name? Available in a growing subset of corridors — UK (CoP), US (EWS), EU VoP-eligible markets, and select APAC corridors (Malaysia, Singapore PayNow, India UPI, Indonesia, Pakistan, Hong Kong).
- Account status: Is the account active, restricted, or closed? Available in select corridors.
When evaluating providers, prioritise the corridors where you have the highest failure rates and the highest payout volumes. A provider with strong coverage in your specific corridor mix is more valuable than broad geographic coverage with shallow depth.
_________________________________________________________
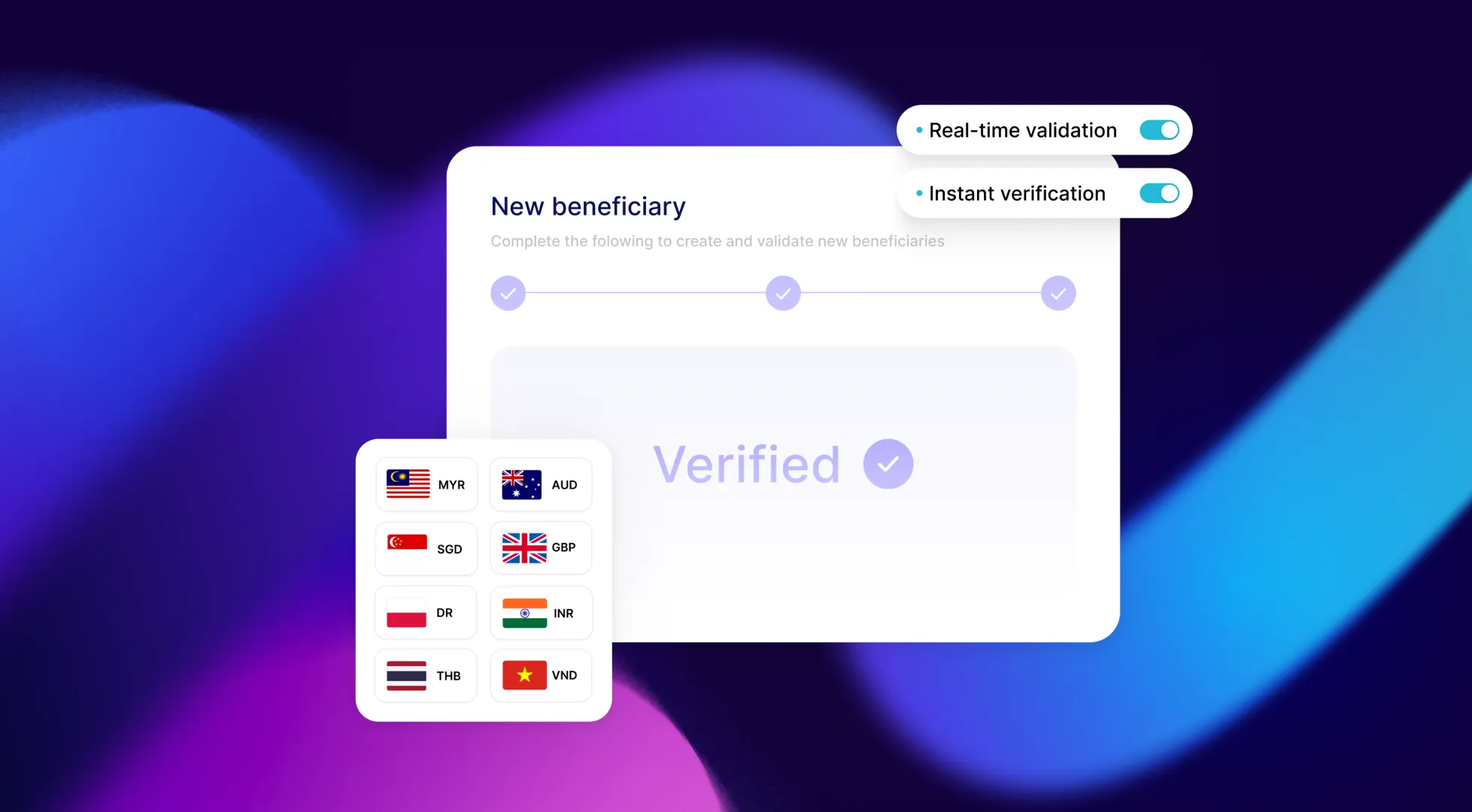
Nium Verify combines coverage, speed, and simplicity
Not all real-time verification is equal. Nium Verify is designed for global payout teams that care about both coverage depth and implementation simplicity:
- Cross-border coverage where it matters most: 30+ countries and currencies with real-time bank account verification, focused on corridors where payout failures and volume are highest.
- Name-match in critical markets: Support for Confirmation of Payee (CoP), VoP-eligible EU markets, and select APAC corridors — helping catch both honest mistakes and payment redirection fraud.
- Verification as a standalone API: Nium Verify can be implemented without migrating your payout rails. It is a thin, independent layer you can drop into existing workflows at onboarding, pre-flight batch, or on-change triggers.
- Actionable response design: Rich response fields (status, failure codes, name-match score, corrected name) are structured to plug directly into routing rules, risk engines, and ops queues.
For most teams, the result is not just fewer failed payouts, but a simpler way to design “no-surprise” payouts into their core product.
_________________________________________________________
Implementation: Go live in under 7 days
For teams integrating bank account verification via API for the first time:
Day 1: API credentials issued. Sandbox access activated. Review API documentation.
Days 2–3: First API calls in sandbox. Test against mock account values for each corridor. Confirm response field handling in your codebase.
Days 4–5: Integration into payout workflow at chosen trigger point (onboarding or pre-flight batch). Error handling and routing logic for each response type.
Day 6–7: QA, testing against edge cases. Sandbox sign-off.
Week 2: Production go-live for target corridor. Monitor: exception rate before/after, ops ticket volume, re-processing rate.
Most teams are live in under 7 days. The integration is not a rip-and-replace — it is a net-new check layered onto the existing workflow.
Typical implementation paths
- Payroll & vendor: Start with 1–2 key corridors where failure rates are highest; wire verification into existing batch job.
- Marketplaces: Add verification to seller payout onboarding in 1 region; roll out globally after NPS impact is proven.
- Fintech/remittance: Begin with first-time payouts to new beneficiaries; expand to recurring flows once impact is validated.
_________________________________________________________
Preventing failures is not a cost - it’s a growth lever
Let’s look at a typical mid‑market EOR platform that processes 8,000 payouts per month across 10–15 countries.
Baseline today
- Monthly payout volume: 8,000 payments
- Current failure rate: 2.0% → 160 failed payments per month
- Share of failures caused by account‑detail issues: ~70% → 112 incidents per month
- Average ops handling cost per exception: $40 (staff time, investigation, re‑processing, customer follow‑up)
That means this team is spending roughly $4,480/month (112 × $40) in manual effort handling preventable failures.
With payment pre-validation
They decide to run pre‑payment account verification on every payout:
- Verification coverage: 100% of payouts (8,000/month)
- Verification cost: $0.25 per payout
- Monthly verification cost: 8,000 × $0.25 = $2,000
By catching invalid or mismatched account details before funds are sent, they eliminate the majority of those account‑detail failures. Even if we only count the 70% of failures we know are addressable via verification:
- Preventable ops cost: $4,480/month
- Verification cost: $2,000/month
- Net saving (ops cost only): $2,480/month
ROI: 124%
Here’s how that breaks down:
- Preventable ops cost: $4,480/month
- Verification cost: $2,000/month
Net saving: $2,480/month
That’s a 124% return, meaning every $1 spent on verification returns ~$2.24 in reduced manual handling costs alone.
This model is conservative. It only includes direct operational savings — not the impact of improved payout success, customer experience, or reduced escalations.
Where teams see the impact
- Payroll & vendor payments: Fewer escalations, cleaner month-end, and less manual rework
- Marketplaces & platforms: Higher seller activation, fewer support tickets, stronger retention
- Fintech & remittance: Higher STP, fewer exceptions, more predictable corridor performance
For payout-driven platforms, reliability isn’t just operational — it’s a growth lever.
Is payment pre-validation a no-brainer for you?
Before your next payout cycle, answer three questions and run one simple formula.
1. Quantify your preventable failures
Formula:
Monthly preventable failure cost
= failures_per_month × %_account_detail_failures × ops_cost_per_exception
If this number is larger than your projected verification cost:
Monthly verification cost
= payouts_per_month × cost_per_verification_call
…then payment pre-validation is economically justified on ops savings alone.
2. Map where bad data enters
At onboarding? In batch uploads? Via bank detail change requests? Each entry point maps to a specific verification trigger (onboarding, pre-flight batch, on-change, hygiene).
3. Apply a simple yes/no checklist
- [ ] You process >5,000 payouts per month, and
- [ ] ≥30% of your returns are due to account detail issues, and
- [ ] Your average handling cost per exception is ≥$15, and
- [ ] You operate in at least one of: UK, US, EU VoP markets, key APAC corridors, and
- [ ] Payout reliability is part of your product promise (payroll, EOR, marketplace, fintech, remittance)
If you tick 3 or more of the boxes above, the economics and experience impact almost always justify moving from detection-after-the-fact to prevention-before-release.
_________________________________________________________
Getting started is straightforward
Calculate your specific savings: Use Nium's Verify ROI Calculator to model your failure rate, ops cost, and verification cost across your specific corridors. Input takes 2 minutes; output is your business case.
Start a pilot: Most teams start with one payout cycle or one corridor. Define a clear before/after metric — exception rate, ops time, re-processing count — and let the numbers make the case.
Talk to us: If you are running recurring payouts to external payees — payroll, vendor payments, marketplace sellers, creator payouts, beneficiaries — and you want to understand what verification coverage looks like for your specific corridors, book a 30-minute conversation.
_________________________________________________________
Nium Verify supports 30+ countries with real-time bank account verification. Available as a standalone API — no payout rails migration required. Integration in 7 days.